Computer Systems Security (Cs-426), PDF, Transport Layer Security


Quantum-resistant Transport Layer Security - ScienceDirect
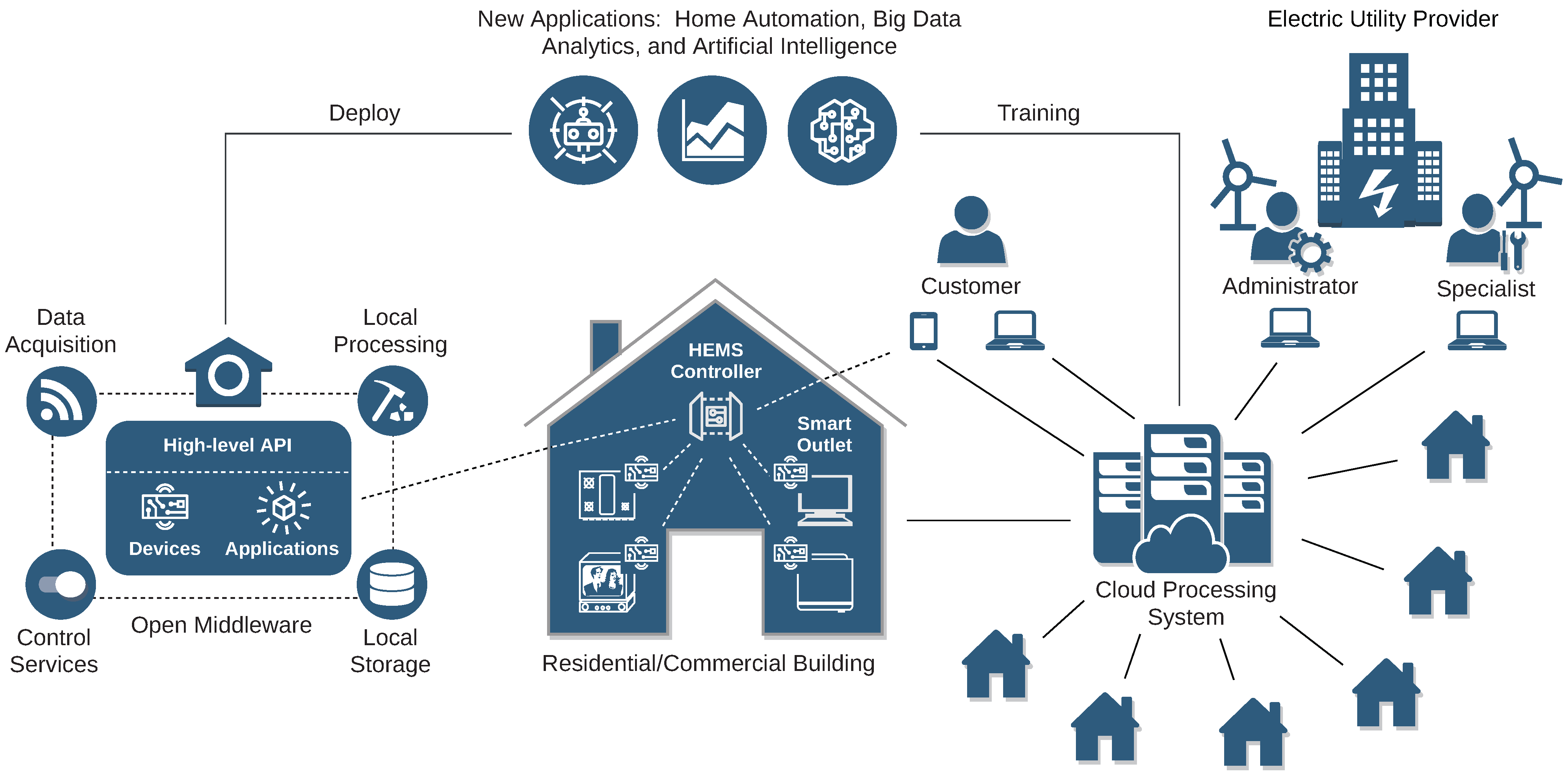
Electronics, Free Full-Text

Quantum-resistant Transport Layer Security - ScienceDirect
PDF) Security of Programmable Logic Controllers and Related Systems: Today and Tomorrow

Cyber-Physical Systems Security: Analysis, Opportunities, Challenges, and Future Prospects
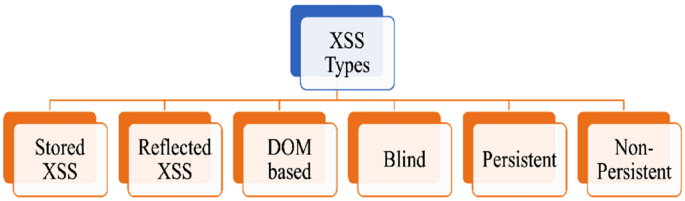
Securing web applications against XSS and SQLi attacks using a novel deep learning approach
Electronics, Free Full-Text

CCSP Certified Cloud Security Professional. Exam Guide [3 ed.] 9781264842292, 1264842295, 9781264842209, 1264842201

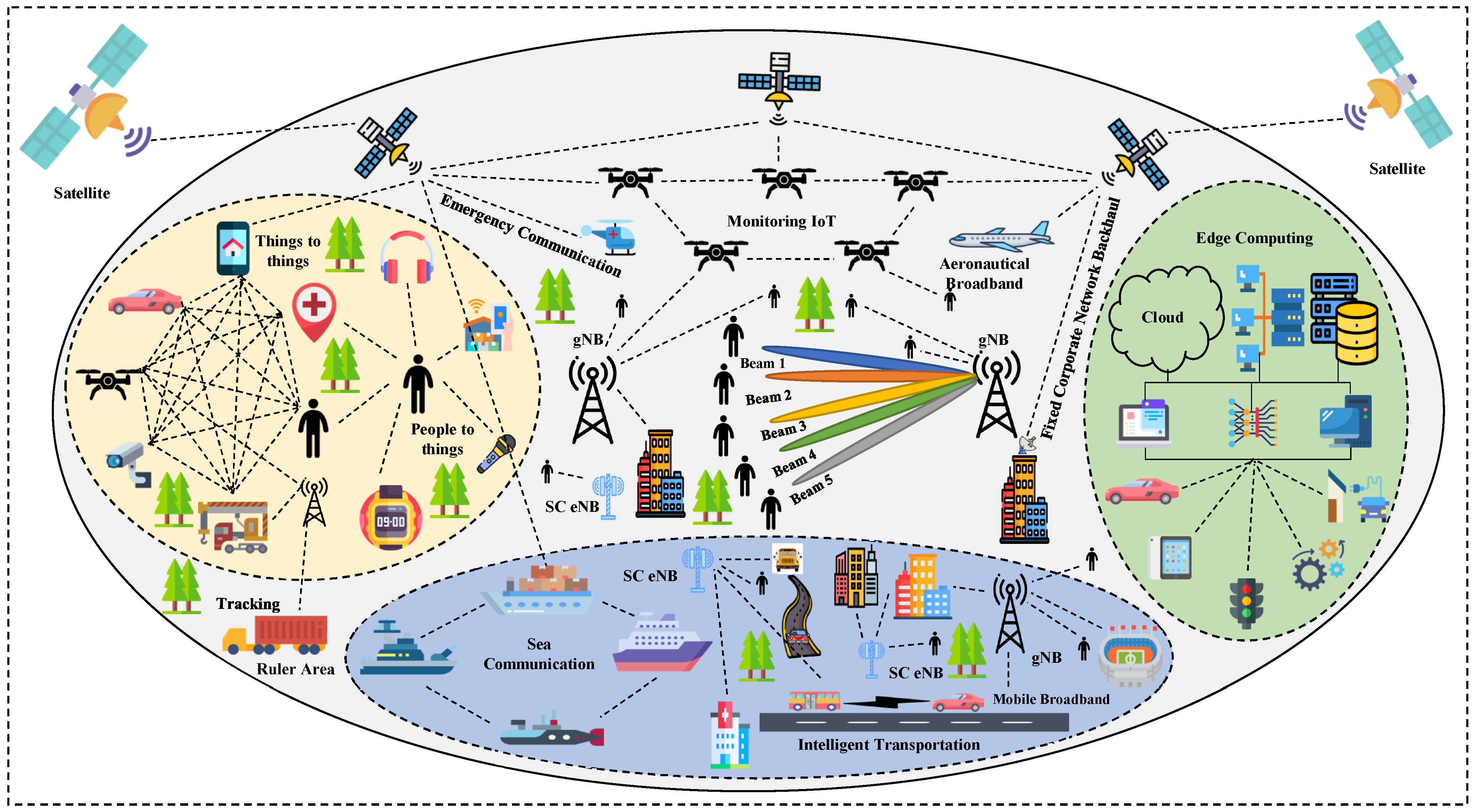
Telecom, Free Full-Text

Designing Automotive ICs For Cybersecurity
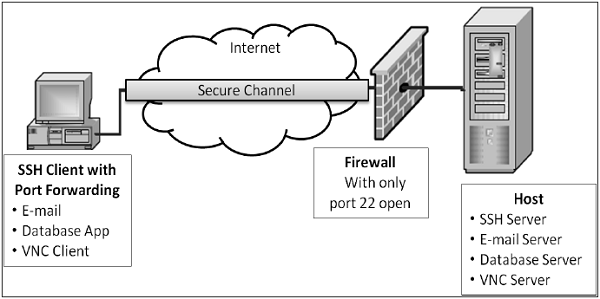
Network Security – Transport Layer
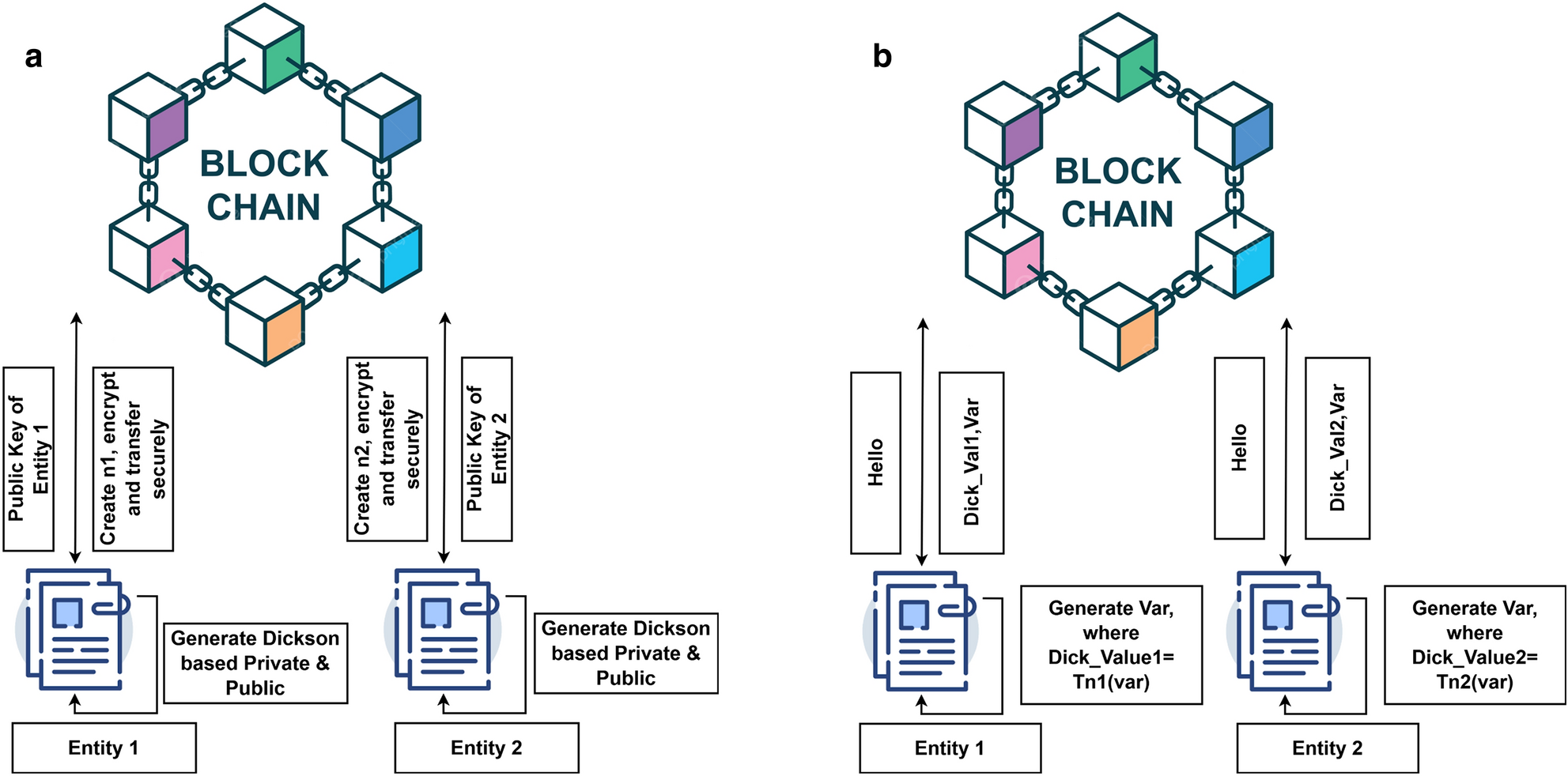
Dickson polynomial-based secure group authentication scheme for Internet of Things

PDF) A Survey on Network Slicing Security: Attacks, Challenges, Solutions and Research Directions

Applied Sciences, Free Full-Text